Own Certificate Authority (CA) SSL installation on Amazon Machine Image (AMI)
1. We need to install HTTPD2.4 package in order to understand the encrypted layer of SSL. Install PHP 5.6 (Apache 2.4 will be automatically installed with this)
# sudo yum install php56
Install important extension for php5.6
#yum install php56-xml php56-xmlrpc php56-soap php56-gd php56-mysqlnd
2. Now we’ll install “mod_SSL”
# yum install mod24_ssl
3. Now we need to install the package “openSSL”, which is used to generate CSR certificate and RSA key.
# yum install openssl
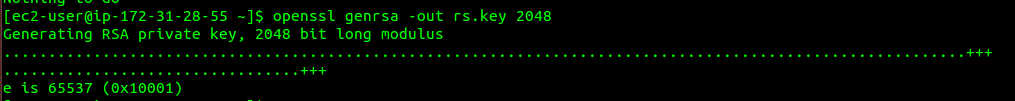
4. Now we’ll generate the Private key with openSSL command.
# openssl genrsa -out rs.key 2048
By above command, We have generated the private key with 2048 bit encryption with name “rs.key”.
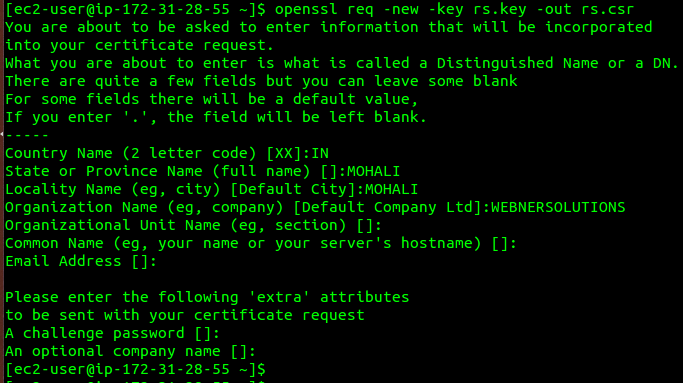
5. Now we’ll create CSR certificate, command is:
# openssl req -new -key rs.key -out rs.csr req -new - it will create new signing request -key pr.key - we need key file to create CSR certificate and we have already generated this key in previous command. -out pr.csr - The name of the certificate will be ‘pr.csr’
After press enter, It will ask to fill some fields like country name, province name, email ID etc. Check following ScreenShot. After that CSR will be generated:
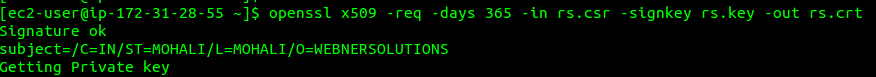
6. Now we’ll generate Self-Signed-Certificate of X509 type which is valid for 365 days.
# openssl x509 -req -days 365 -in rs.csr -signkey rs.key -out pr.crt
7. After certificate files are created, we’ll copy them and place them at right location.
# cp pr.crt /etc/pki/tls/certs # cp pr.key /etc/pki/tls/private/ # cp pr.csr /etc/pki/tls/private
8. Now open the secure web server configuration file and edit the line number 106 and 113 as showing in following screen shot.
# vim /etc/httpd/conf.d/ssl.conf
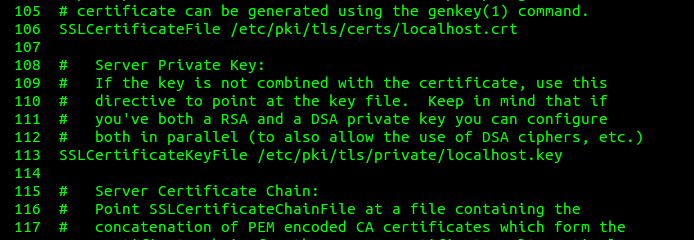
Replace these lines with following lines.
SSLCertificateFile /etc/pki/tls/certs/rs.csr SSLCertificateKeyFile /etc/pki/tls/private/rs.key
Now you can check the parameters are right or not by following command.
# httpd -t
Output should be “Syntax OK” like below screenshot
![]()
9. Configure Apache web server file.
# vim /etc/httpd/conf/httpd.conf
<VirtualHost *:443>
ServerName domainname.com
ServerAdmin webmaster@itmanx.com
SSLEngine on
SSLCertificateFile /etc/pki/tls/certs/rs.crt
SSLCertificateKeyFile /etc/pki/tls/private/rs.key
DocumentRoot /var/www/html/
</VirtualHost>
10. Add the port number 443 in the Inbound security groups and then restart the HTTPD service.
# sudo /etc/init.d/httpd restart
